In the high-stakes arena of enterprise B2B procurement, social proof has evolved from a marketing “nice-to-have” into the fundamental Trust Operating System (TOS) of the organization. As we navigate 2026, the traditional siloed approach to testimonials is dead. High-ticket decisions are no longer made by individuals; they are adjudicated by a complex Decentralized Decision-making Unit (DMU) where each stakeholder—the CTO, CFO, CMO, and CEO—requires a different dialect of evidence to bypass their internal skepticism.
To win at this level, an organization must transition from “collecting quotes” to Engineering Multi-Stakeholder Proof. This is the science of synchronizing technical data, institutional reputation, and verifiable outcomes into a singular, unassailable narrative of success.
The collapse of monolithic trust
The “one-size-fits-all” case study is the primary point of failure for legacy B2B brands. A document that satisfies a CMO’s desire for “brand alignment” often triggers an immediate veto from a CTO looking for “architectural resilience.” This disconnect creates a Trust Vacuum, where the more you try to prove your value through generic praise, the more suspicion you generate within the technical and financial layers of the C-suite.
The stakeholder-specific validation crisis
In 2026, the enterprise buyer is suffering from extreme “Validation Fatigue.” They are bombarded by marketing fluff and automated review volume that lacks the granular detail required for institutional risk mitigation.
- The CTO rejects emotional narratives in favor of Technical Proof Videos (TPV) and raw logs.
- The CFO ignores qualitative praise, demanding the BIO (Baseline-Intervention-Outcome) framework to calculate true ROI.
- The Head of Security requires the Ghost Reference Protocol to ensure that technical success doesn’t compromise confidentiality.
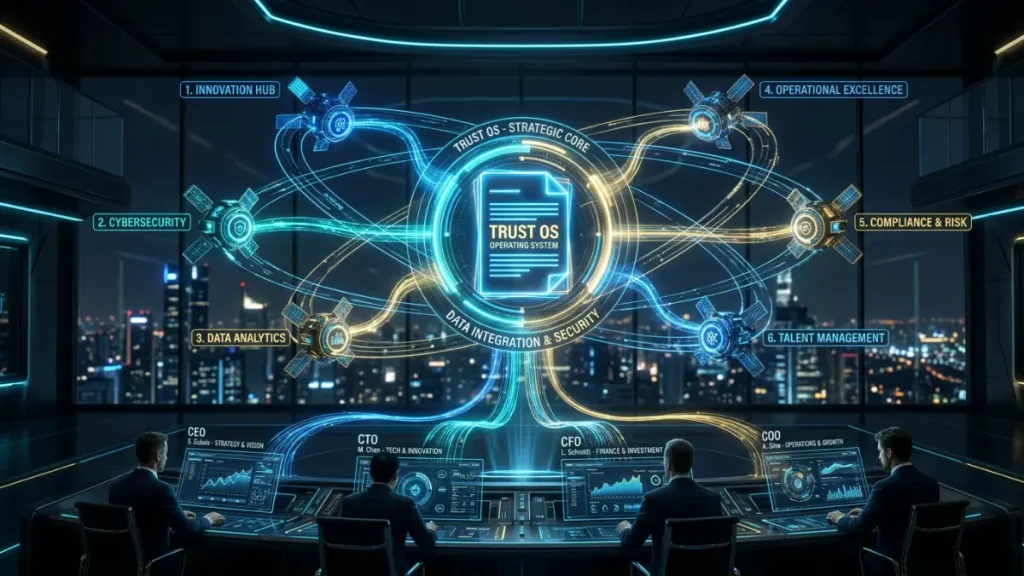
Social proof as the “Trust Operating System”
We must redefine social proof. It is no longer a collection of static assets; it is a dynamic, multi-layered infrastructure. Like a modern OS, your social proof must manage permissions (confidentiality), execute logic (data-backed claims), and provide a seamless interface for different users (stakeholders). When social proof is engineered as a system, it neutralizes the cognitive dissonance inherent in complex sales, moving the conversation from “Why should we trust you?” to “How quickly can we integrate?”
The three pillars of the High-Fidelity Proof Engine
To build a “Trust Operating System” that survives the scrutiny of the C-suite, the organization must master three distinct dimensions of evidence:
1. Technical Verifiability: The end of the “Black Box” claim
For the technical gatekeeper, trust is a function of transparency. This is why scaling social proof harvest destroys authenticity when it lacks technical depth. The science of proof requires a move toward Ledger-Validated Outcomes. By utilizing blockchain or private timestamped ledgers to secure your BIO framework metrics, you provide a level of “Hard Proof” that is immune to marketing manipulation.
2. Institutional Sovereignty: Leveraging the Human-Expert Proxy
The most powerful trust signal in 2026 is not the company logo; it is the Sovereign Expert. As established in the LinkedIn authority gap, the C-suite trusts practitioners, not brands. Your Proof Engine must empower your internal experts to act as “Trust Proxies.” When your Lead Architect breaks down a stealth sector implementation on a peer-to-peer level, they provide a form of social proof that no corporate white paper can replicate.
3. Environmental Abstraction: The “Stealth Authority” advantage
The pinnacle of the High-Fidelity Proof Engine is the ability to validate expertise without breaching NDAs. In high-concurrency or defense sectors, your most powerful successes are often invisible. This is where leveraging silent social proof in stealth sectors becomes a strategic weapon. By using Environmental Archetypes instead of client names, you signal to the C-suite that you respect the “Sanctity of the Data.”
The Operational High-Fidelity Stack: feeding the Trust OS
A strategic vision is useless without a data-capture engine. To build a multi-stakeholder narrative, the organization must move beyond “Case Study Interviews” and implement Automated Evidence Mining via the Third-party review stack.
Automated Signal Capture (The “Proof Intake”)
By integrating Gong.io or Chorus with your CRM, you capture “Unfiltered Truth.” When a client mentions a technical hurdle overcome during a renewal call, that verbatim is a gold mine. This raw data is then processed through the BIO framework, stripping away the marketing fluff to leave only the high-density metrics that convince a CFO.
From Raw Data to Verified Assets
The 2026 standard for proof engineering requires a “Truth Loop.” Data captured via UserEvidence or technical logs is automatically formatted into Technical Proof Assets. These are “Verification Units.” Each unit is timestamped and, for top-tier accounts, secured via a Blockchain Ledger to ensure that the authenticity of the soul remains intact even as you scale.
The C-Suite Proof Matrix: Engineering trust by persona
The core of the “Science of Proof” is Contextual Delivery. To close the LinkedIn authority gap, you must deploy the right proof to the right gatekeeper.
The Deployment Matrix
| Stakeholder | Primary Psychological Friction | Required Proof Asset | Strategic Anchor |
| CTO / Architect | Technical Feasibility & Debt | Technical Proof Video (TPV) | Raw Dashboards & “Scars” |
| CFO / Procurement | ROI & Financial Risk | BIO Framework Ledger | Audited Outcome & Data Indexing |
| CEO / Founder | Market Leadership & Vision | Sovereign Expert Insights | Human-Led Authority & Peer Proof |
| CSO / Security | Compliance & Data Integrity | Ghost Reference Protocol | Environmental Abstraction |
Neutralizing the “Veto Power”
Every enterprise deal has a “Silent Veto.” Often, it comes from a stakeholder who was never invited to the demo but who reviews the “Proof Packet.” By providing a pre-engineered matrix of evidence, you neutralize these vetoes before they happen. You provide the CTO with the CLI logs and the CFO with the normalized performance curves, ensuring that the cognitive dissonance never has a chance to stall the contract velocity.
The Proof Maturity Model: From Logo-Centric to Proof-Centric
To transition from a legacy B2B marketing organization to a 2026 authority powerhouse, the C-suite must sponsor a shift toward Proof Engineering maturity.
- Stage 1: Reactive Case Study (The Legacy Trap): Social proof is a post-sale “nice-to-have,” resulting in generic PDFs full of marketing fluff.
- Stage 2: Active Evidence Collection (The Operational Shift): Implementation of the Operational Tech Stack and extraction of technical verbatims.
- Stage 3: Engineered Social Proof (The Trust OS): Integration into the product lifecycle. Every technical success triggers an automated BIO framework capture, validated via Blockchain to combat Proof Decay.
Engineering the irreversible close
In high-ticket enterprise B2B, social proof is not about making the buyer feel good; it is about making them feel secure in their decision. The science of multi-stakeholder social proof converts institutional trust into a competitive moat.By building a dynamic Trust Operating System that speaks the specific language of the CTO, CFO, CMO, and CEO, you bypass cognitive dissonance, eliminate silent vetoes, and accelerate contract velocity. In 2026, you cannot purchase trust; you must engineer it. Organizations that master this high-fidelity evidence architecture will not only win the market—they will own the authority of the sector.
